As you may know Forefront TMG Beta 3 includes outbound HTTPS Inspection.
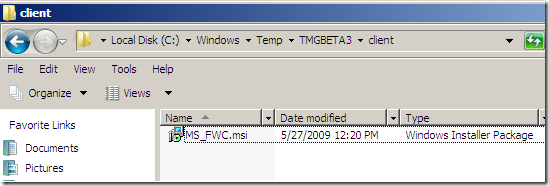
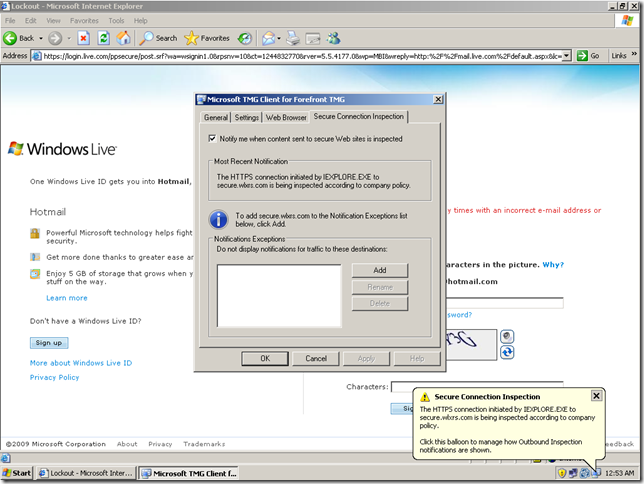
With the help of the Firewall Client we can notify the users that their HTTPS connections are being inspected(the Microsoft TMG Client for Forefront TMG can be found within the location where the downloaded TMG Beta 3 .exe file was extracted):
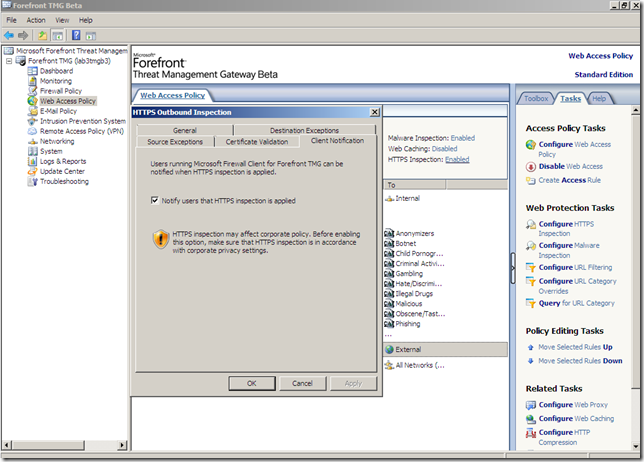
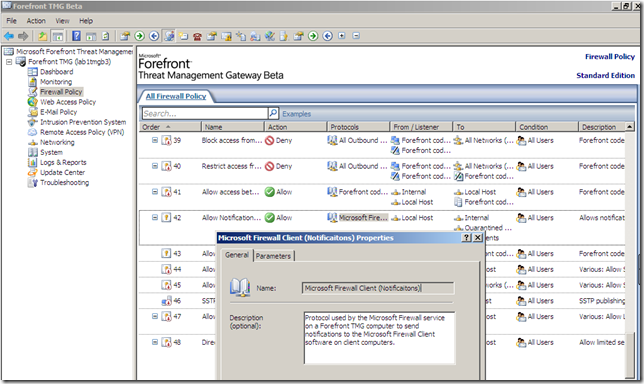
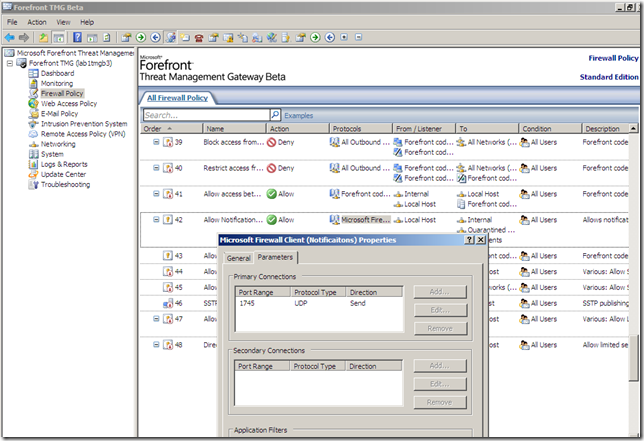
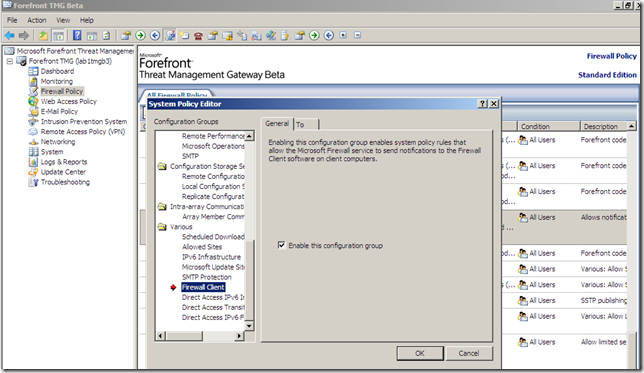
A system policy is enabled:
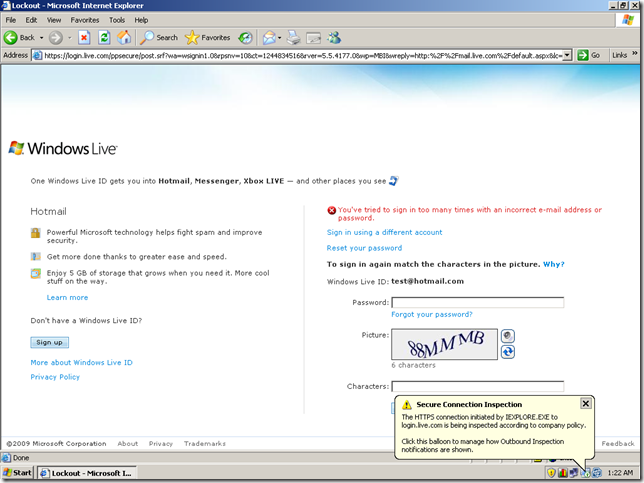
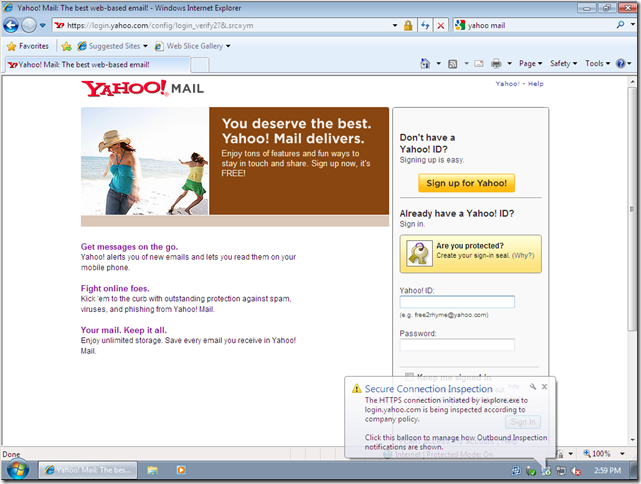
How the notification looks like at this moment ?
See it yourself:
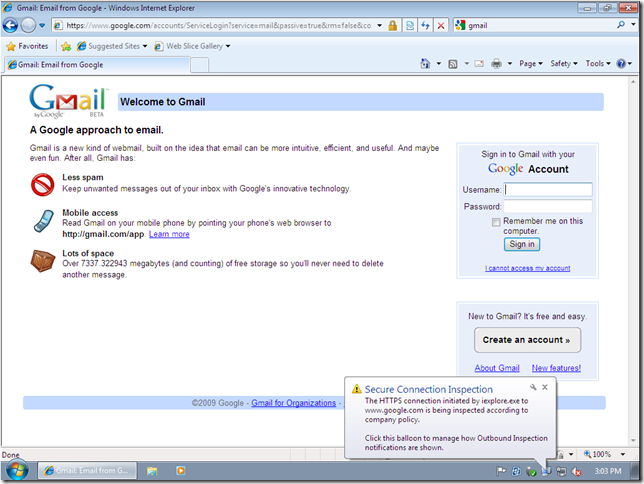
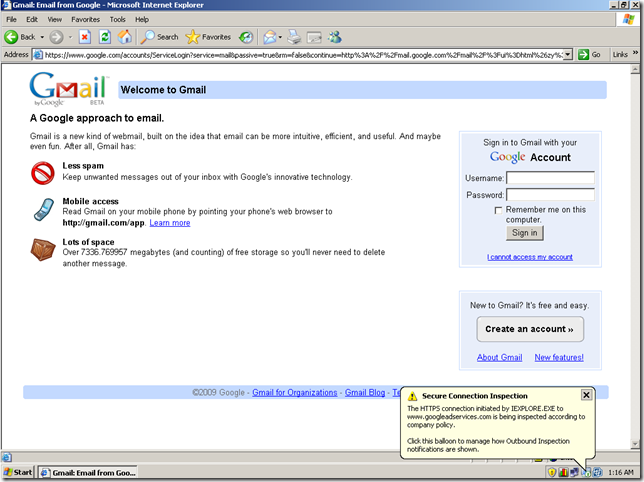
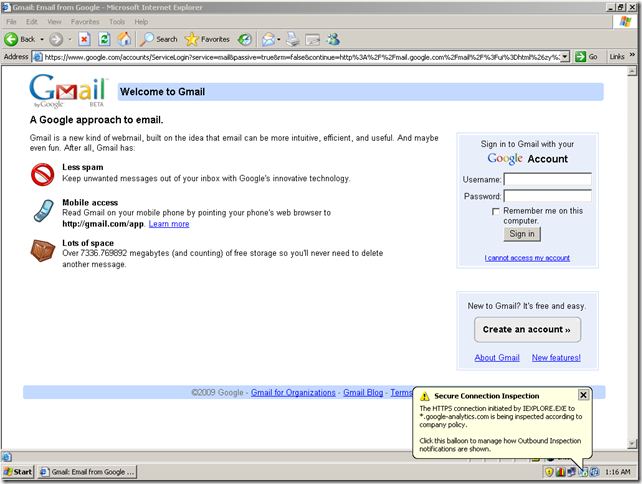
And it’s interesting to see what we would normally not see, for example while accessing Gmail, in the “background” we have other HTTPS connections:
I must say I’m not sure exactly right now how the notifications work(the help files do not include many details at this moment), but I did not get any notifications until I configured on the browser the TMG Beta 3 machine as a web proxy, so basically my client was a web proxy client + firewall client + secure NAT client.